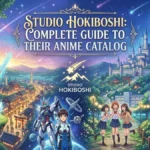
SSIS 469 Error: How to Fix “Connection Already in Use”
Introduction I’ve spent the last several years building and troubleshooting ETL pipelines with SQL Server Integration Services, and the SSIS ...
Read more
What Is Gizmocrunch.com? Inside the Growing Tech Blog

Technology journalism has transformed dramatically in the past decade. Once dominated by large media outlets with dedicated hardware reviewers and ...
Read more
Keine Karriere-Subdomain Gefunden: Meaning, Causes and Fixes

I would answer the searcher’s question plainly at the start: “keine karriere-subdomain gefunden” means a system looked for a dedicated ...
Read more
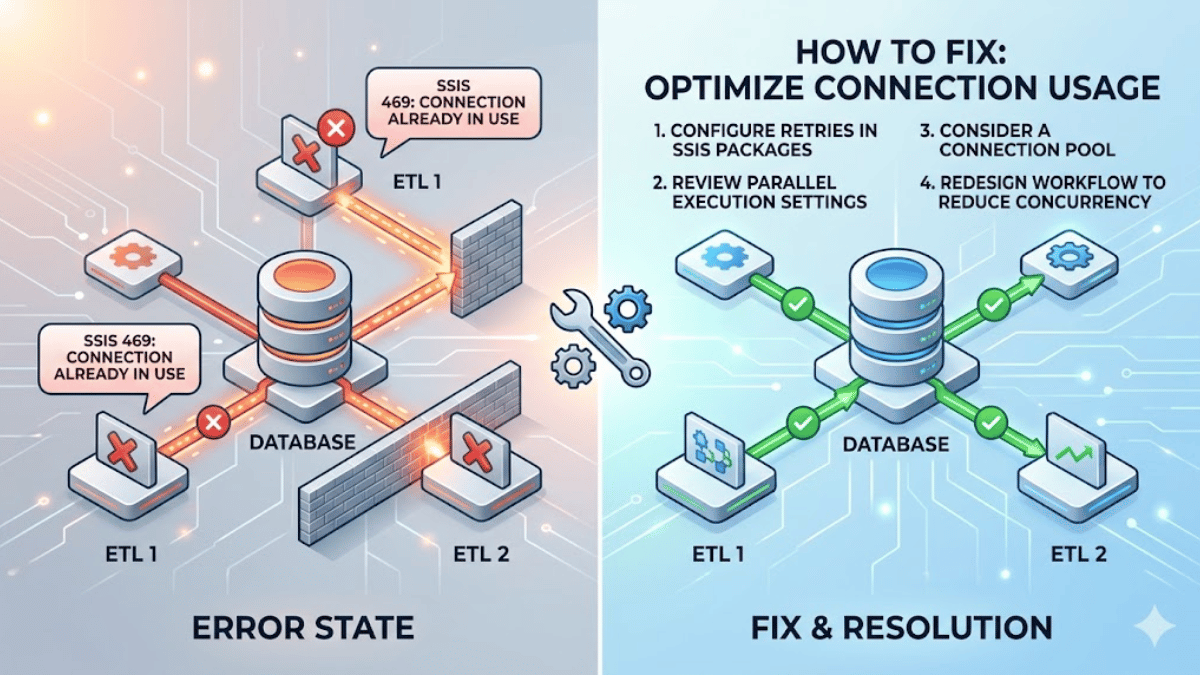
Ziperto ROM Site Explained: Safety, Risks and Legality
I remember the moment I first searched online for an old console game that had disappeared from official stores. The ...
Read more
Home Hypackel Explained: Organization and Browser Games

I first noticed the phrase “Home Hypackel” while researching everyday productivity habits and digital culture. The term appears in two ...
Read more
What Is 51chigua? Inside China’s Gossip Web

I first encountered the term “51chigua” the same way millions of internet users encounter it: through a shared link promising ...
Read more
Spinbet99 and the Rise of Online Casino Platforms

Online gambling has transformed dramatically over the past two decades, evolving from simple digital card games into sophisticated ecosystems of ...
Read more
Pinkchyu Leaks and the Digital Privacy Debate

When I first encountered the search phrase “pinkchyu leaks,” the immediate question was simple: What happened? For many readers, that ...
Read more
Zumikami: Exploring the Digital Identity Behind the Name
When I first typed “zumikami” into a search bar, I was looking for something concrete: a biography, a brand, perhaps ...
Read more
FBI Warns iPhone Android Scams: Stay Safe Now

I have seen how quickly mobile scams evolve, and it is clear that smartphone users must stay alert every single ...
Read more