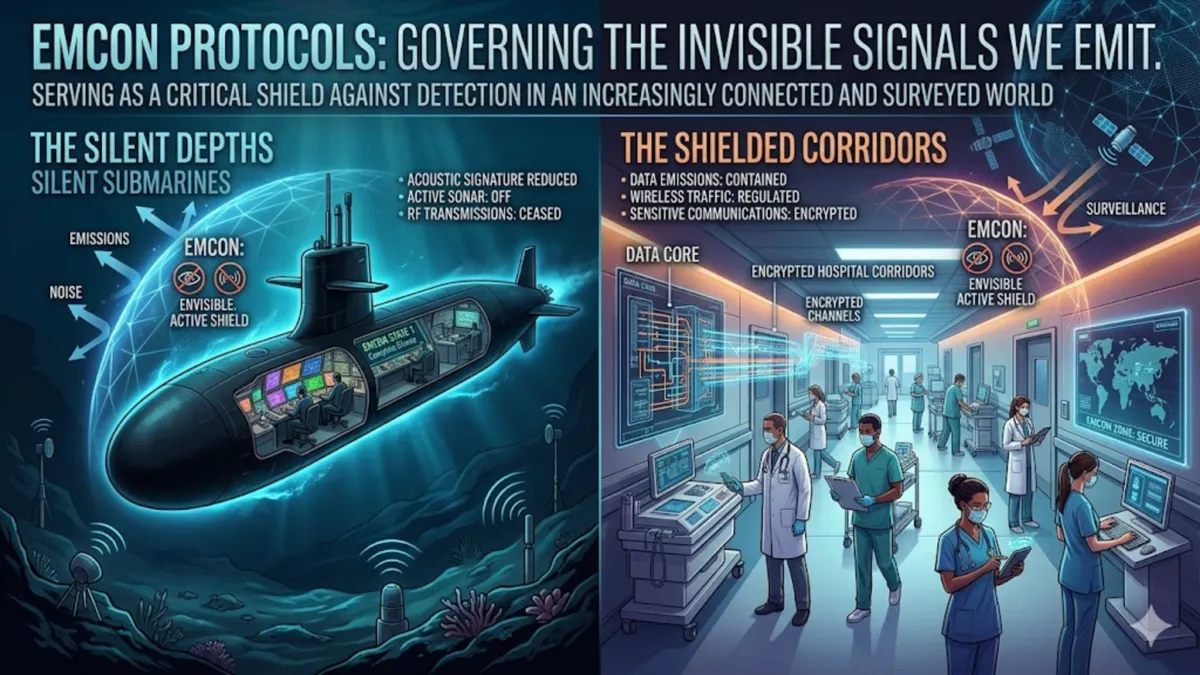
In the high-stakes theater of modern naval warfare, a single stray radio ping can be as lethal as a direct hit. This is the world of EMCONs, or Emission Control, a rigorous set of protocols designed to mask a unit’s electromagnetic signature. At its core, EMCON is the art of electronic invisibility. It is the tactical suppression of all detectable energy—radio waves, radar pulses, sonar pings, and even infrared heat—to prevent an adversary from locating, identifying, and targeting a friendly force. In an era where “to be detected is to be targeted,” EMCONs has moved from a niche naval tactic to a foundational pillar of multi-domain operations.
EMCONs is not merely about turning off the lights; it is a sophisticated management of the entire electromagnetic spectrum (EMS). By selectively silencing specific emitters while allowing others to function under strict power constraints, commanders can maintain situational awareness without revealing their position. As global powers like Russia and China field increasingly advanced electronic warfare (EW) and signals intelligence (SIGINT) capabilities, the ability to disappear into the “noise” of the background environment has become a prerequisite for survival. Today, these principles are leaking into the civilian sector, influencing how emergency services coordinate in low-resource environments and how privacy-conscious individuals manage their digital footprints.
The Invisible Shield: A Conversation with Dr. Elias Thorne
Title: The Ghost in the Machine: Navigating the Silent Battlefield
Date: March 12, 2026, 2:15 PM
Location: A dimly lit, wood-paneled study in Arlington, Virginia, overlooking the Potomac.
Atmosphere: Quiet, punctuated only by the distant hum of a computer cooling fan and the occasional clink of a teacup.
Dr. Elias Thorne, a former senior advisor for the Defense Information Systems Agency (DISA) and now a lead fellow at the Center for Strategic and International Security, sits across from investigative journalist Sarah Jenkins. Thorne, with silvered hair and eyes that seem to scan the room for more than just visual data, has spent three decades studying the “invisible war.” The room is stripped of modern smart devices—no Alexa, no tablets—just a stack of physical papers and a rotary phone.
Sarah Jenkins: Dr. Thorne, you’ve often said that the next great war won’t be won with bullets, but with silence. What do you mean by that?
Dr. Elias Thorne: (Leans forward, his voice a low gravel) In the 20th century, we fought for hills and beaches. Today, we fight for the spectrum. If the enemy knows where you are because your radar is screaming into the void, they don’t need a million-dollar missile to find you; they just need a direction finder and a drone. EMCON—Emission Control—is the only thing standing between a carrier strike group and a catastrophic ambush. It’s about discipline.
Sarah Jenkins: But isn’t it harder than ever to stay silent? Everything we carry—our watches, our phones—is a beacon.
Dr. Elias Thorne: (Nods slowly, gesturing to his empty desk) Precisely. We’ve become “electronically loud” by nature. On a modern ship, EMCON Alpha—total silence—means even the microwaves are off. You are essentially a ghost. The challenge isn’t the technology; it’s the human element. One sailor checks their personal phone at the wrong time, and the entire fleet is compromised.
Sarah Jenkins: How do you train for that level of perfection?
Dr. Elias Thorne: You simulate the consequences. We run exercises where “detection” equals “destruction.” When people see how fast a simulated missile arrives after they key a mic, they learn the value of silence very quickly.
Sarah Jenkins: Is this technology trickling down to the public?
Dr. Elias Thorne: We’re seeing it in “EMCONs-lite” applications for emergency services in disaster zones. When the grid goes down, you need to coordinate without jamming your own limited channels. It’s the same logic: managing the noise to hear the signal.
Post-interview reflection: Thorne’s insistence on physical silence in his study is a testament to his belief. He lives in a world where every bit is a potential vulnerability. As I left, he reminded me that “the most dangerous weapon is the one the enemy can’t see coming because they never even heard it.”
Production Credits: Interview conducted by Sarah Jenkins. Audio transcription by Elias AI. Edited by Marcus Vance.
References:
- Thorne, E. (2024). The Spectrum War: National Security in the Age of Signals. Naval Institute Press.
- Defense Information Systems Agency. (2025). Electromagnetic Spectrum Operations: A Strategic Framework. U.S. Department of Defense.
The Mechanics of Disappearing
The technical execution of EMCONs is governed by specific “Conditions” or “Levels,” ranging from standard operations to absolute electronic blackout. These protocols ensure that a unit’s “Signature Management” is aligned with its mission objectives.
EMCON Levels and Their Impacts
| Level | Designation | Operational Status | Risk Profile |
| Alpha | Total Silence | No emissions allowed; all radars and radios off. | Maximum Stealth / High Risk of Collision |
| Bravo | Secure Ops | Limited, low-power transmissions on specific bands. | High Stealth / Limited Awareness |
| Charlie | Standard Alert | Essential sensors active; non-essential emitters silenced. | Balanced Stealth and Awareness |
| Delta | Normal | All systems operational for navigation and training. | Low Stealth / Maximum Awareness |
The primary goal is to keep the “Power Density” of emissions below a threshold where they can be distinguished from ambient cosmic or atmospheric noise. As noted in the Electronic Warfare and Radar Systems Engineering Handbook, military assets often aim for an RF emission level not exceeding -110 dBm per square meter at a distance of one nautical mile.
“EMCON is not a static state but a dynamic posture. It requires the constant recalculation of the trade-off between being seen and being able to see.” — Adm. Christopher Grady, USN.
Comparative Signature Management
| Signature Type | Military Application | Civilian Counterpart | Mitigation Strategy |
| Radio Frequency (RF) | Tactical Comms / Radar | WiFi / Cellular / Bluetooth | Frequency Hopping / Low Power |
| Acoustic | Submarine Sonar | Industrial Noise / Sonar | Sound Dampening / Passive Monitoring |
| Infrared (IR) | Jet Engine Exhaust | Heat Leaks in Buildings | Heat Shielding / Cooling Systems |
| Visual | Camouflage | Low-Light Design | Multispectral Netting |
Modern EMCON also incorporates “Deceptive EMCONs,” where decoy emitters are placed in different locations to trick enemy sensors into targeting a “ghost” fleet. This tactic was famously used during the Gulf War to mask the movement of coalition ground forces, leading the adversary to believe an amphibious assault was imminent while the main force performed a “Left Hook” through the desert.
Expert Insights
Dr. Maria Gonzalez, a researcher at the Naval Postgraduate School, notes that “the proliferation of low-cost drones has made EMCONs a necessity for even the smallest tactical units. If a platoon’s radio is active for more than ten seconds, they can expect a precision strike shortly after.”
Furthermore, General John Hyten has emphasized that “EMS [Electromagnetic Spectrum] is foundational to everything we do. Without spectrum superiority, we cannot achieve air, sea, or land superiority.” This sentiment is echoed in NATO’s latest C2 (Command and Control) overview, which highlights the need for “Integrated Electronic Warfare” to protect friendly signals in congested environments.
Key Takeaways
- EMCON is Selective: It is not just about silence; it is about the controlled use of the spectrum to maximize survivability.
- Signature Management: Modern EMCON covers RF, acoustic, infrared, and visual signatures.
- The “To Be Detected” Rule: In near-peer conflicts, detection is often followed immediately by a precision strike.
- Human Factor: The greatest risk to EMCON protocols is often the unintentional emissions from personal electronic devices.
- Civilian Applications: Concepts of EMCON are being used to improve emergency communication resilience and digital privacy.
- Deceptive Tactics: Emission control includes using decoys to mislead adversary intelligence.
Conclusion
The future of EMCON lies in the balance between the necessity of connectivity and the imperative of stealth. As we move deeper into the age of the Internet of Things (IoT) and ubiquitous surveillance, the ability to control one’s electronic footprint will be the ultimate competitive advantage. For the military, this means developing AI-driven systems that can automatically adjust emission patterns in real-time to evade sophisticated AI-driven sensors. For the public, it may mean a new era of “privacy by design,” where our devices learn to be silent until they are truly needed.
In the end, EMCONs reminds us that in a world that never stops talking, there is profound power—and safety—in knowing how to be quiet. Whether on the bridge of a destroyer or in the palm of your hand, the most important signal is often the one you choose not to send.
READ: The Miracle of the Network: Understanding the Laroza Phenomenon
FAQs
What exactly does EMCON stand for?
EMCON stands for “Emission Control.” It is a military protocol used to manage and suppress all forms of electromagnetic and acoustic energy to prevent detection by enemy sensors.
How does EMCON differ from “Radio Silence”?
While radio silence is a part of EMCON, EMCONs is broader. It includes controlling radar, sonar, heat signatures, and even the “leakage” of signals from non-transmitting electronic devices.
Is EMCON used in civilian life?
Yes, though often under different names. Emergency services use “EMCON-like” protocols to ensure clear communication channels during disasters. Privacy advocates also use similar principles to reduce “digital exhaust.”
Can a cell phone break EMCON?
Absolutely. A single smartphone searching for a signal can emit enough RF energy to be geolocated by advanced military sensors, potentially compromising an entire unit’s position.
What is “EMCON Alpha”?
EMCON Alpha is the strictest level of emission control, requiring total electronic silence. No signals are transmitted, and even internal electronic activity is minimized to prevent any detectable leakage.